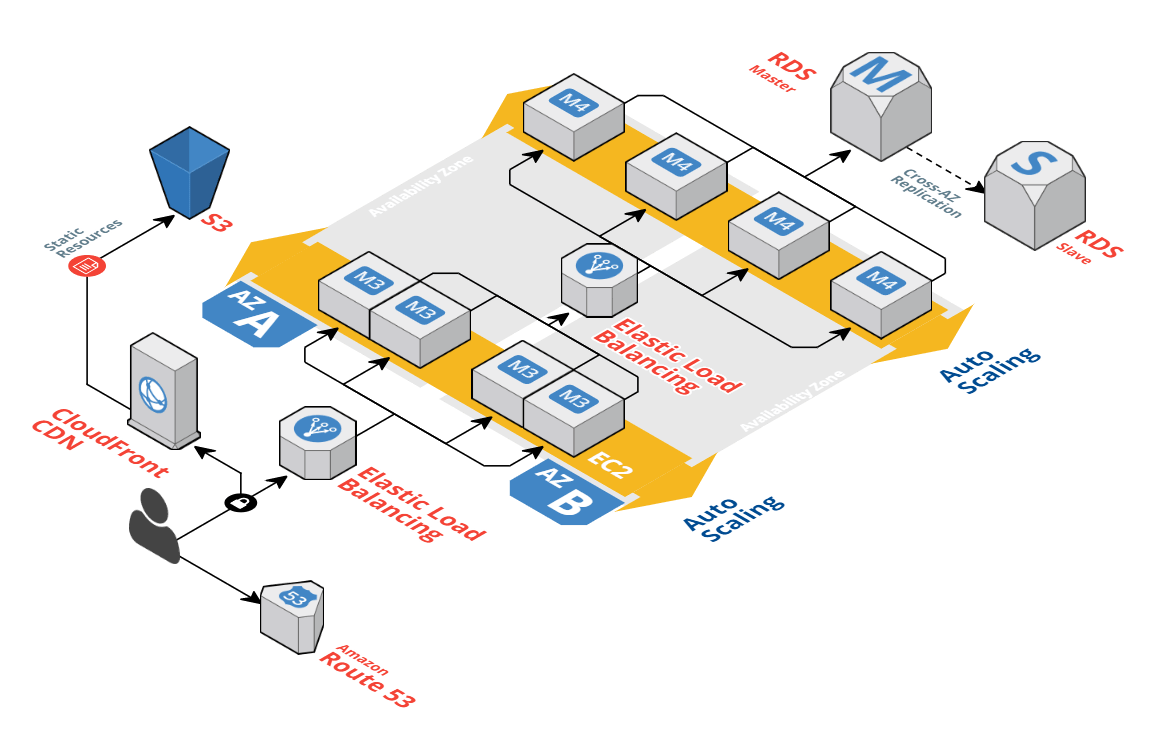
Cloud Architecture
Our team is experienced with containerizing workloads, and using higher-level orchestrators to bake in scalability, monitoring, and fault tolerance.
We're heavy users of serverless and optimization around cloud-native serverless workloads.
Build on your existing on-premise infrastructure while harnessing the flexibility of public cloud offerings.
Migration Paths
DevOps
Builds-as-a-service. Increase sprint velocity and developer productivity with automated build pipelines on every code change.
Automatic or human-signed deploys to any application or environment. Drastically reduce your Time To Release.
Reduce risk by running unit and integration tests performantly on every commit.
Security, Compliance & Monitoring
Architect your cloud deployment for end-to-end security, OWASP vulnerabilities, and cloud-specific attack vectors
Monitored, self-healing deployments with compliance guardrails baked in.
Monitor application metrics for security & performance (APM). Log and search everything.